

Hacking campaign uses infected James Webb Telescope image
source link: https://siliconangle.com/2022/08/31/hacking-campaign-uses-infected-james-webb-telescope-image/
Go to the source link to view the article. You can view the picture content, updated content and better typesetting reading experience. If the link is broken, please click the button below to view the snapshot at that time.

Hacking campaign uses infected James Webb Telescope image
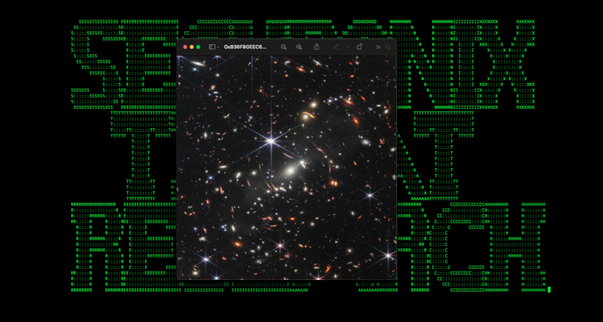
A newly discovered hacking campaign is exploiting an image from the James Webb Telescope to infect targets with malware.
Detailed today by researchers at Securonix Inc. and dubbed “GO#WEBBFUSCATOR,” the campaign leverages a deep field image taken from the telescope and obfuscated Golang programming language payloads to infect a potential victim.
The infection vector starts with a phishing email containing a Microsoft Office attachment containing an external reference hidden inside the document’s metadata which downloads a malicious template file. When the document is opened, the malicious template file is downloaded and saved on the system, initiating the first stage of code execution for the attack.
Eventually, the script downloads a JPEG image that shows the James Webb Telescope deep field image. The image contains malicious Base64 code disguised as an included certificate, which is then decrypted and saved into a built-in Windows executable called “msdllupdate.exe.”
The generated file is a Windows 64-bit executable about 1.7 megabytes in size and employs several obfuscation techniques to hide from antivirus software and to make analysis difficult. “At the time of publication, this particular file is undetected by all antivirus vendors,” the researchers note.
“It’s clear that the original author of the binary designed the payload with both some trivial counter-forensics and anti-endpoint detection and response detection methodologies in mind,” the researchers added.
The researchers conclude that the methodology used in the attack chain is interesting. Although the use of Golang is not uncommon, its combination, in this case, with the Certuitil command-line program is much less common.
“This campaign once again proposes the risk inherent in the concept of digital trust and its implications in the field of security,” Paolo Passeri, principal sales engineer at cybersecurity software company Netskope Inc., told SiliconANGLE.
Referencing the growth of remote work, Passeri noted that “users now place more reliance on digital interactions than on human ones, which lowers the level of guard against any content coming from the internet and are no longer used to thoroughly check the origin of the information.”
Image: Securonix
A message from John Furrier, co-founder of SiliconANGLE:
Show your support for our mission by joining our Cube Club and Cube Event Community of experts. Join the community that includes Amazon Web Services and Amazon.com CEO Andy Jassy, Dell Technologies founder and CEO Michael Dell, Intel CEO Pat Gelsinger and many more luminaries and experts.
Join Our Community
Click here to join the free and open Startup Showcase event.
We really want to hear from you, and we’re looking forward to seeing you at the event and in theCUBE Club.
Click here to join the free and open Startup Showcase event.
Recommend
About Joyk
Aggregate valuable and interesting links.
Joyk means Joy of geeK