

VMware搭建内网渗透环境 - 林烬
source link: https://www.cnblogs.com/LeslieSec/p/17028722.html
Go to the source link to view the article. You can view the picture content, updated content and better typesetting reading experience. If the link is broken, please click the button below to view the snapshot at that time.
VMware搭建内网渗透环境
网络结构:
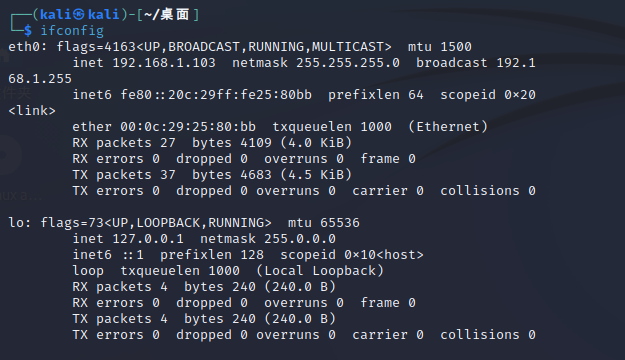
攻击机:kali 192.168.1.103
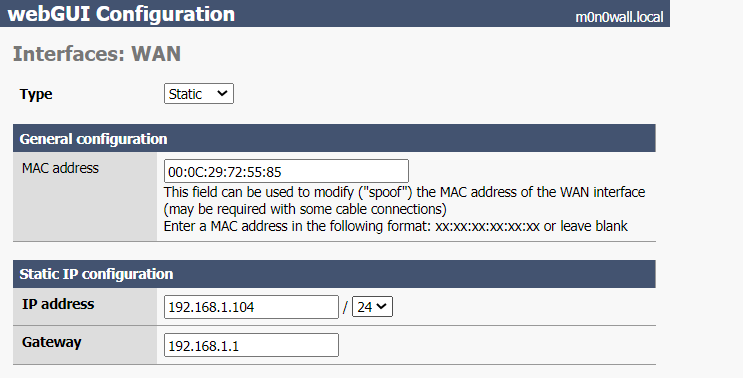
DMZ区域:防火墙 WAN:192.168.1.104 LAN:192.168.10.10
winserver03 LAN:192.168.10.11
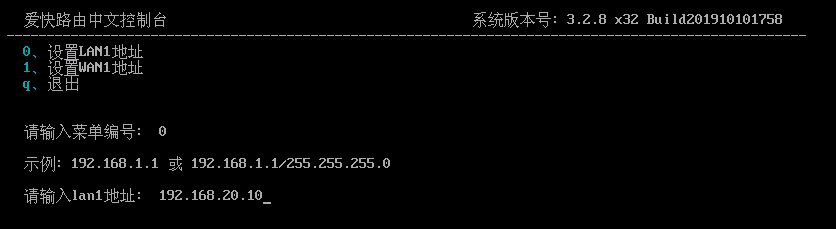
用户办公区域:路由器 WAN:192.168.10.20 LAN:192.168.20.10
winserver08 LAN:192.168.20.100
核心文件区域:路由器 WAN:192.168.20.20 LAN:192.168.30.10
redhat LAN:192.168.30.100
搭建过程:
将桥接物理网段设置为公网网段,这边选用kali攻击机,所以需要将kali的网络连接状态设置为桥接模式,复制物理网络连接。
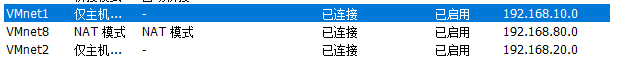
模拟内网中的网段环境,比如说,将vmnet1设置为10网段,将vmnet2设置为20网段
1.搭建dmz区域
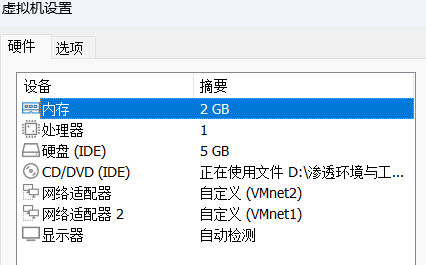
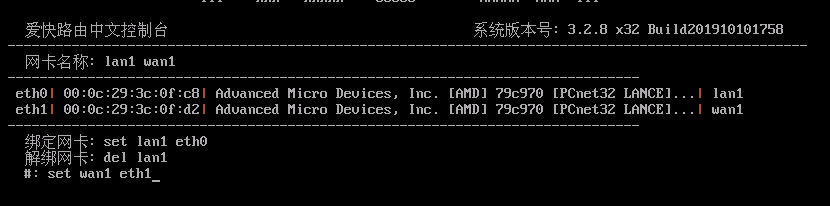
安装一个防火墙,模拟公司内网与外部通信得情况,防火墙设置为双网卡结构,其中一张网卡模拟与外部通信,直接桥接物理网络的状态,另外一张网卡模拟与内部通信,连接到vmnet1网卡上。这边选用generic-pc-1.8.1.iso作为防火墙。
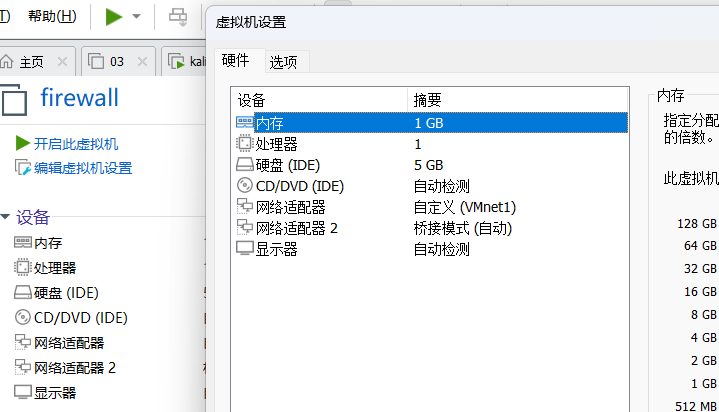
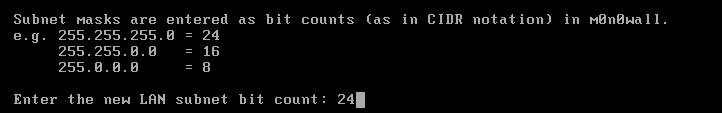
将IP地址192.168.10.10作为内网的网关地址,并且给定24位的子网掩码
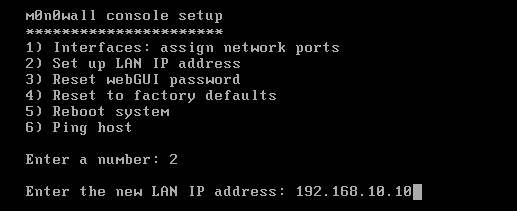
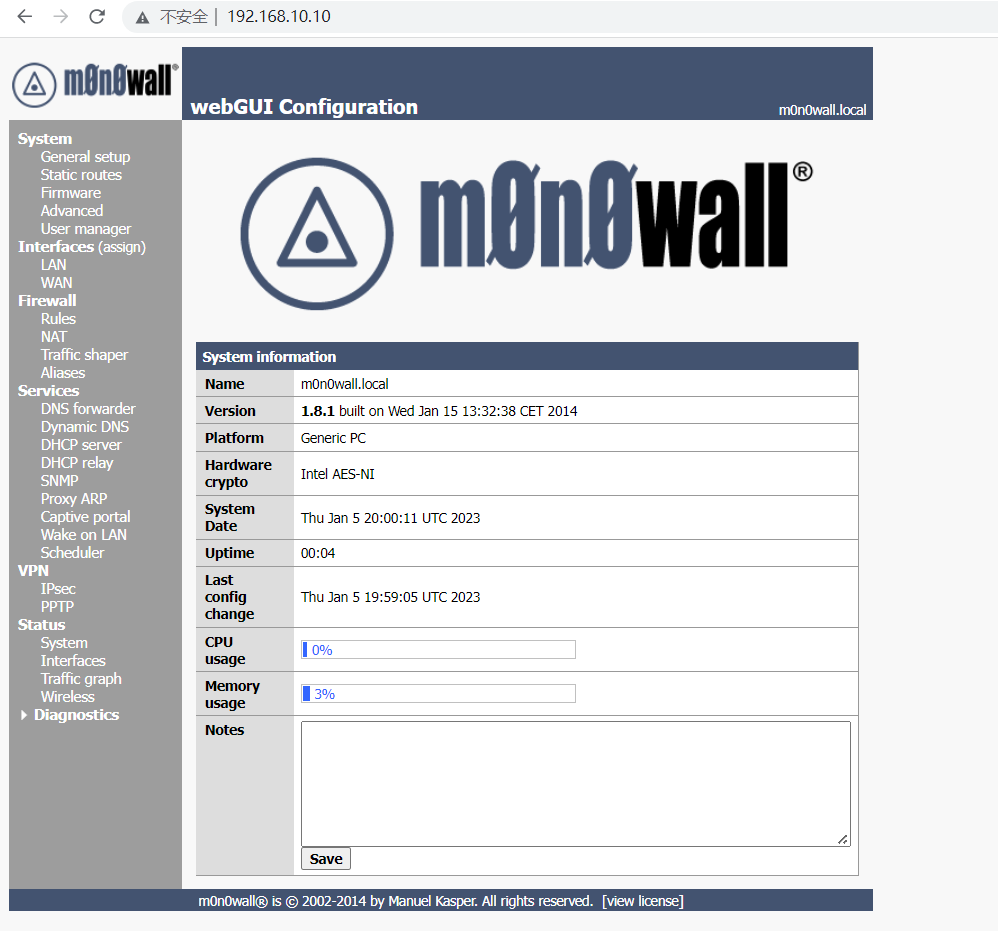
配置完成,访问192.168.10.10即可到达防火墙管理界面
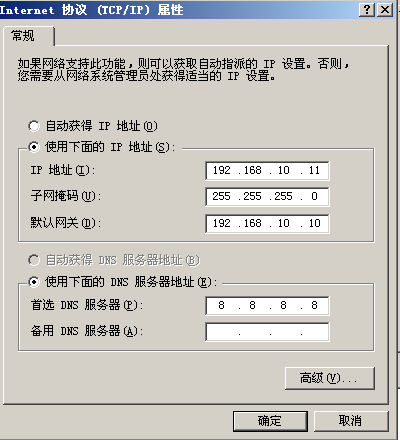
然后将windows server 03 加入到10网段中,以下是03机器的网络配置。物理机访问192.168.10.11:8006进行测试

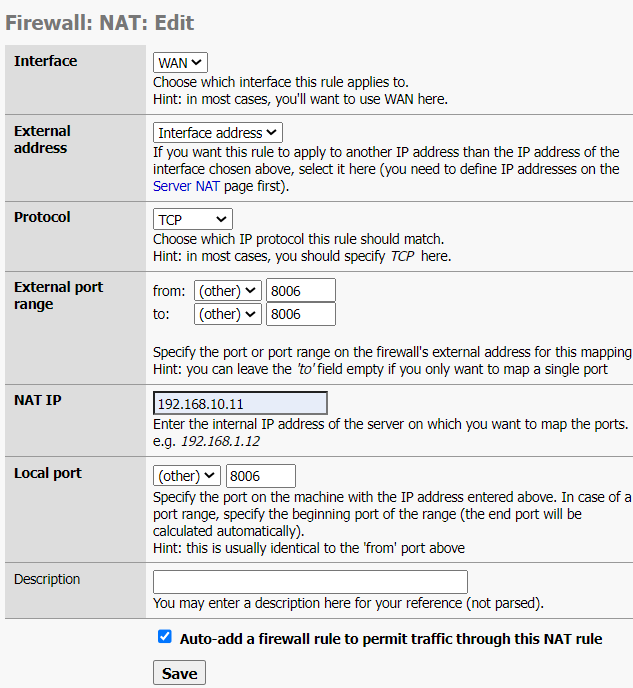
然后在防火墙中,将192.168.10.11:8006映射出来,这样可以让外部使用192.168.1.104:8006进行访问
wan口配置设置,通向公网
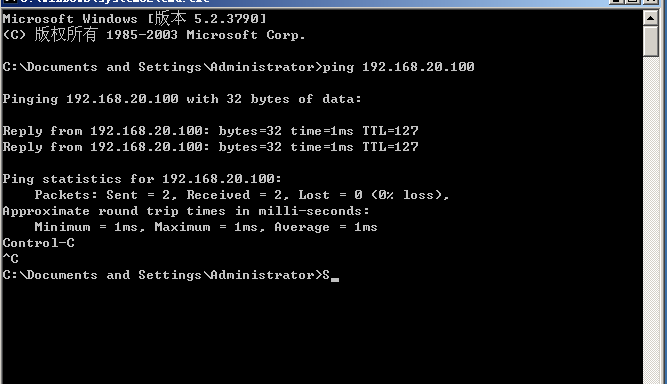
访问成功,成功把内网vmnet1的ip地址映射到公网ip上

2.搭建用户办公区域
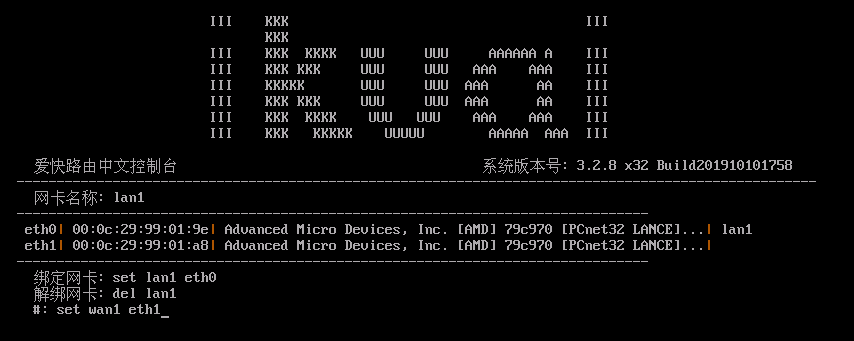
搭建路由,路由的一张网卡连接DMZ区域,所以使用vmnet1,一张网卡连接用户办公区域,使用vmnet2
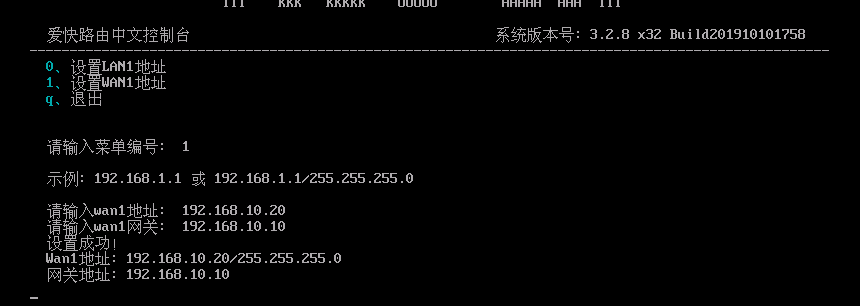
设置路由器的公网和内网地址
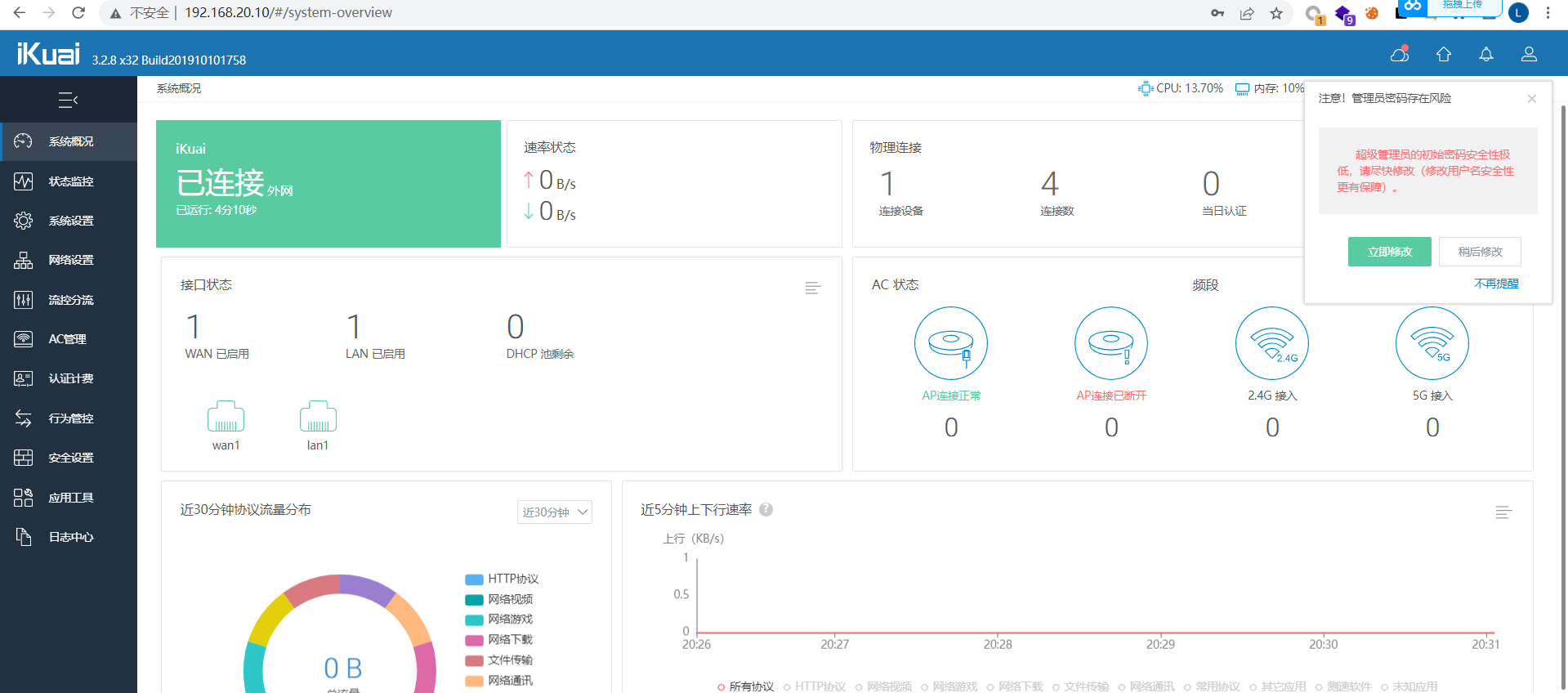
登录后台查看是否分配成功
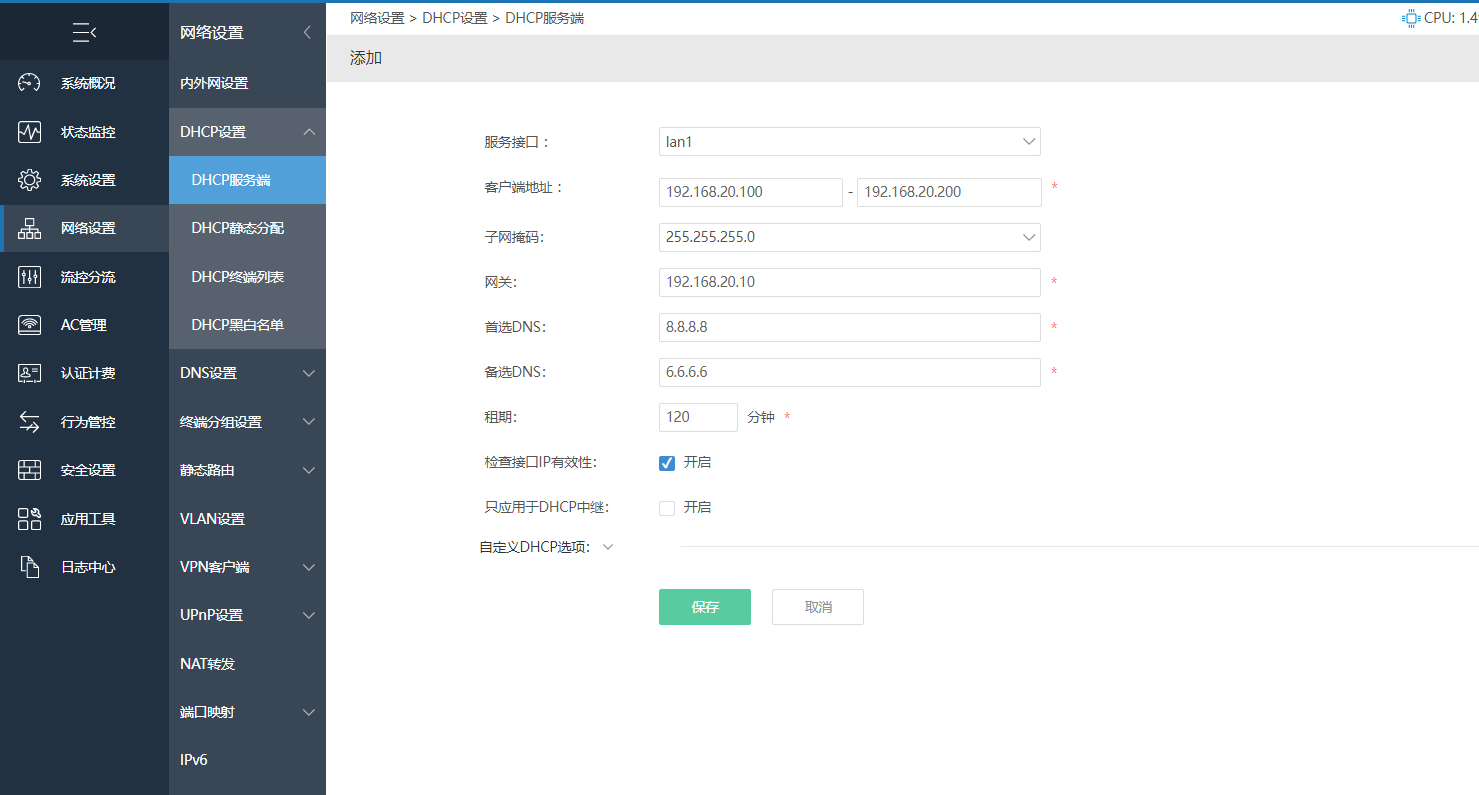
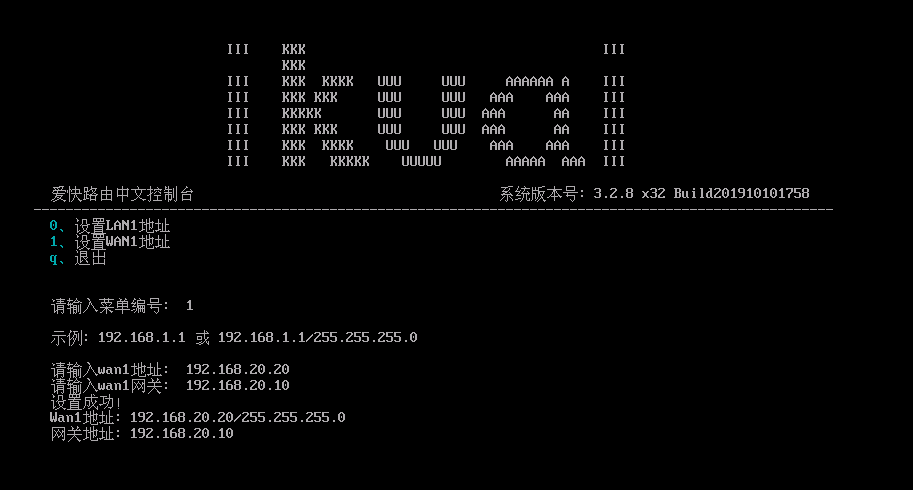
设置路由器的DHCP池
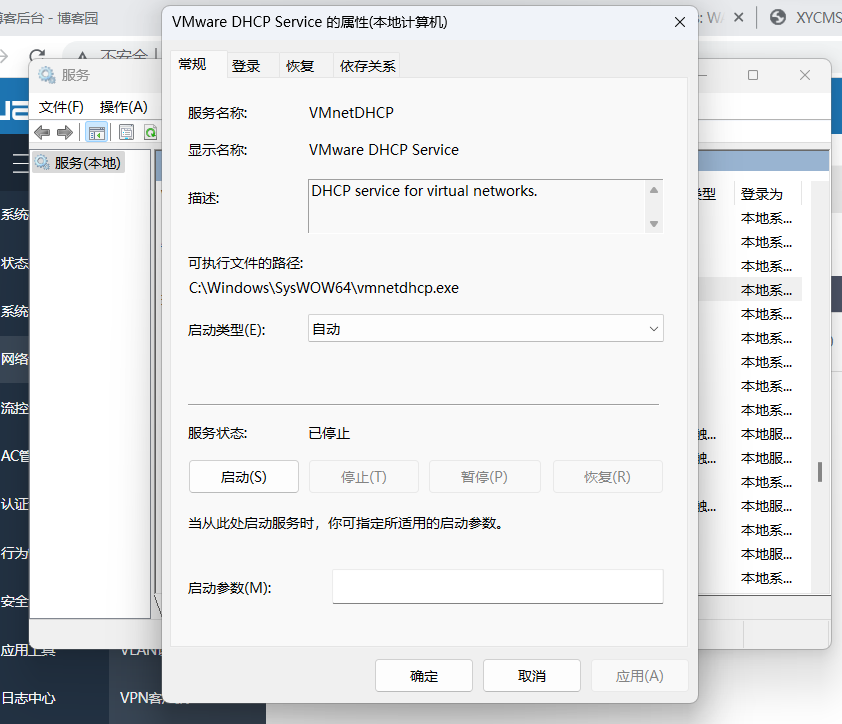
关闭vm自带的DHCP分配,以免产生冲突
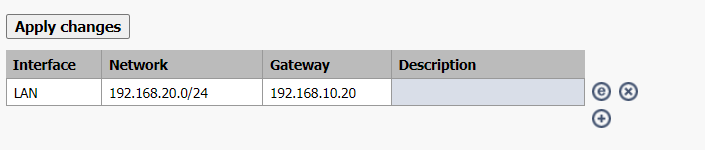
此时将08的ip改成自动获取,可以看到,ip地址是路由器自动分配的20网段,此时的08服务器的网站得网络是怎么产生的呢,其实是08服务器发起请求,然后交给了路由器,路由器再通过wan口交给了防火墙,防火墙与外部通信之后,将返回的结果传回给了08服务器,网络就这么产生了。但是这时候会发现,20网段的机器和10网段的机器并没有交互,这是因为所有的请求都直接交给了防火墙,所以如果需要20网段的机器和10网段的机器通信,那么需要在防火墙中设置路由表的下一跳位置为路由器,那么防火墙就会把请求交给路由器,路由器就可以和20网段的机器进行通信。

3.核心文件区
新建vmnet3,用来分配核心文件区域的IP

第一张网卡为连接用户办公区域的网卡,第二张网卡连接核心数据区
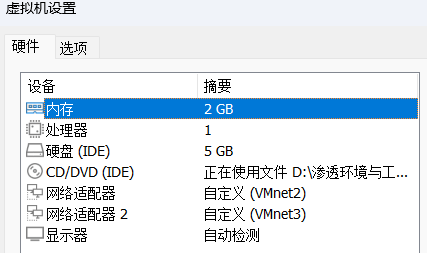
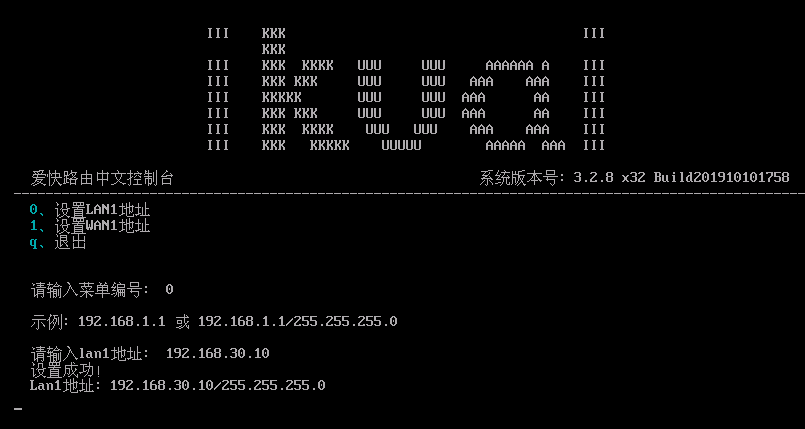
同上进行路由器设置
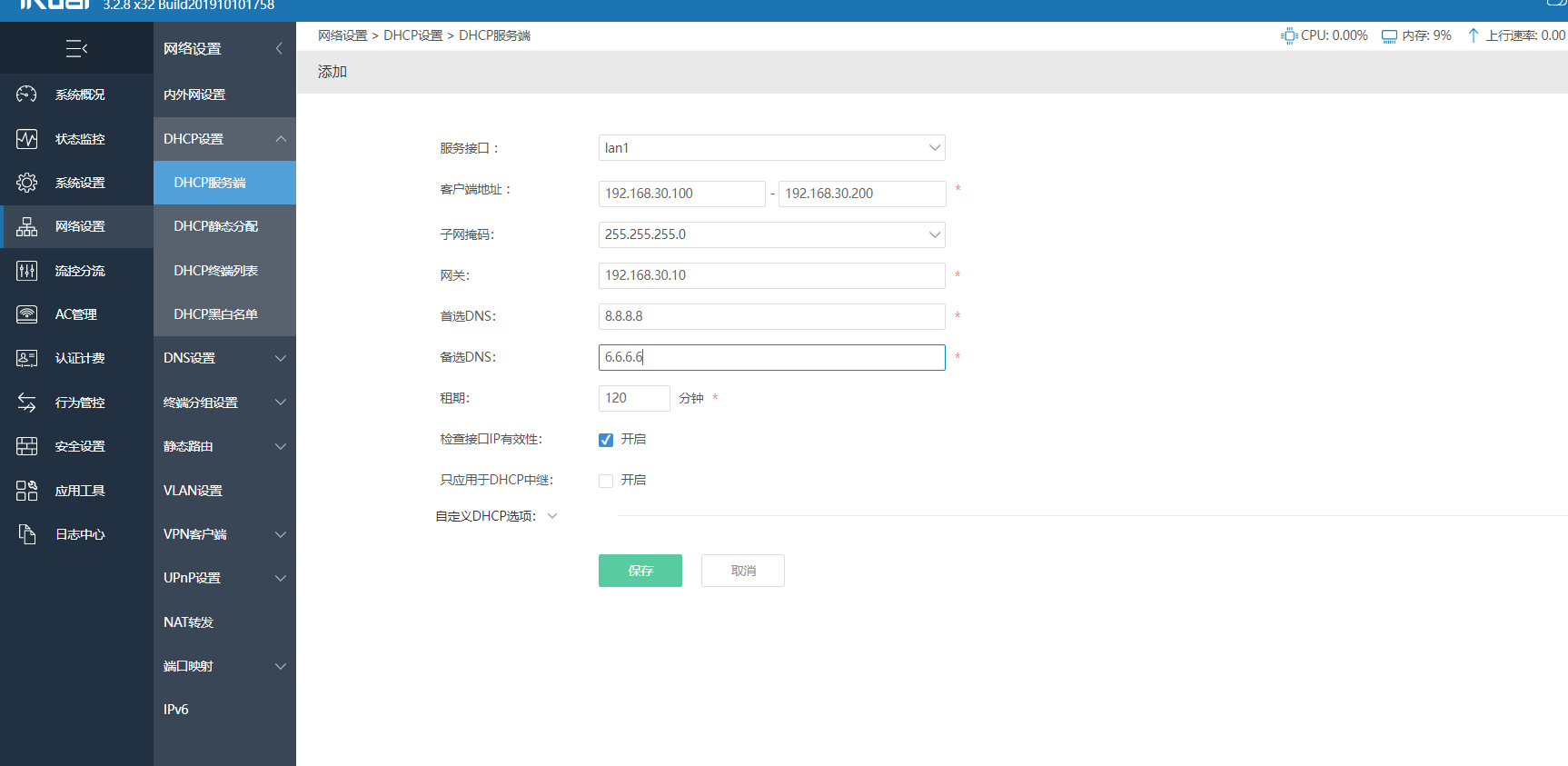
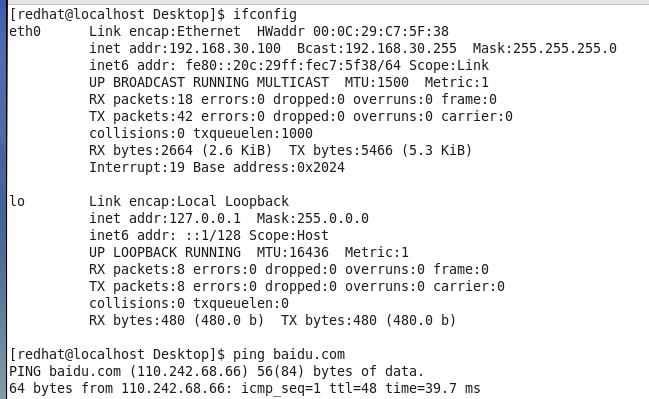
可以看到,在核心数据区的redhat机器已经被分配了30.100的网段地址
在防火墙将30网段的地址分发给第一个路由器
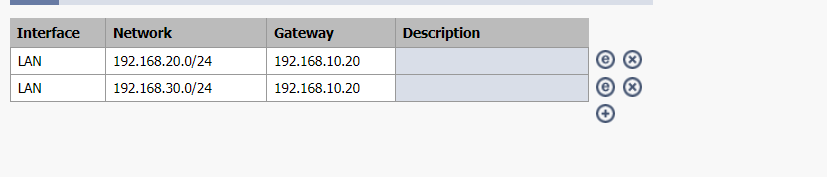
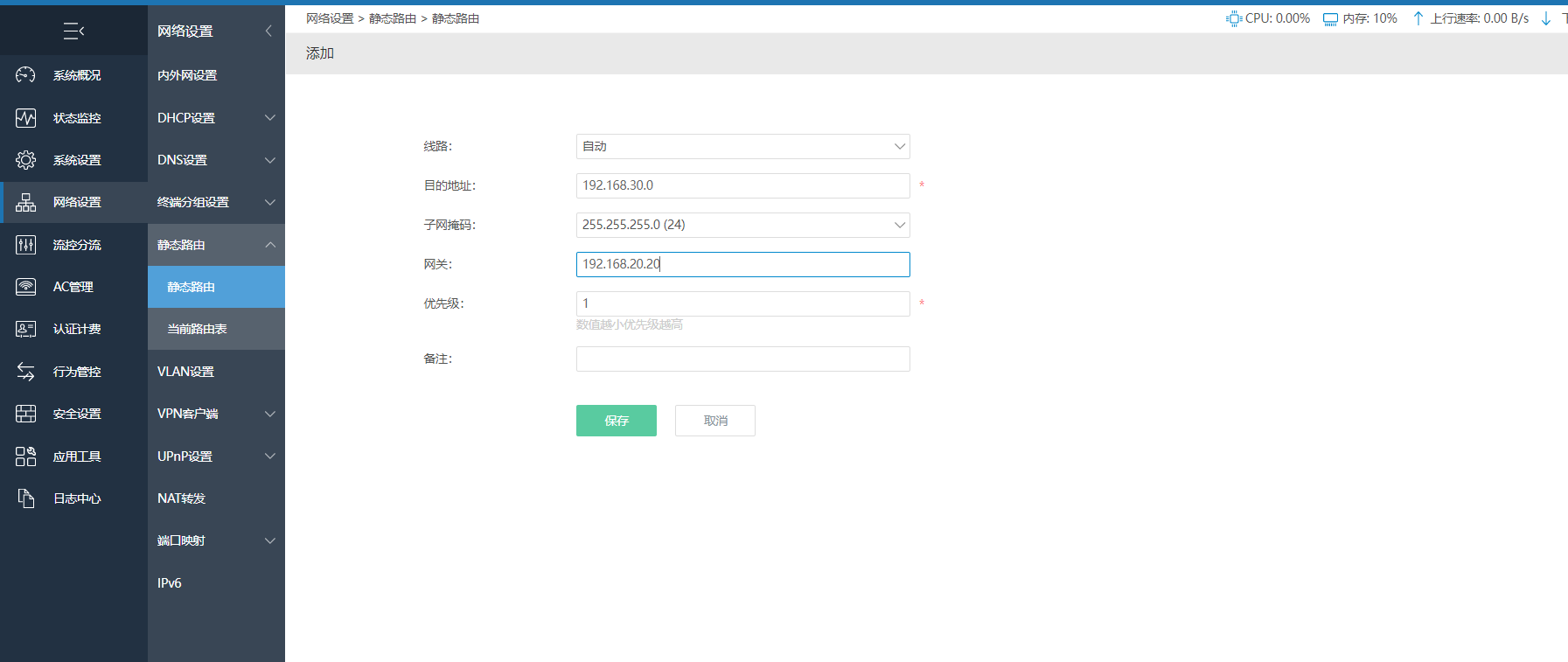
在第一个路由器中,将30网段的请求分发给第二个路由器
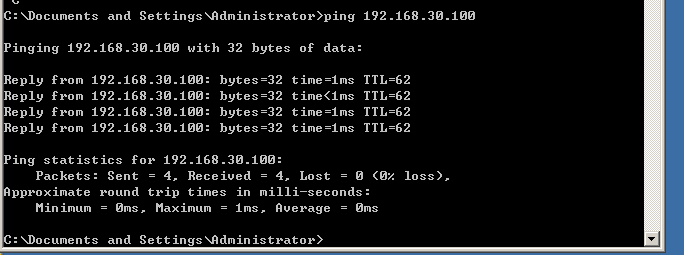
从而实现三个区域之间的网络互通
Recommend
About Joyk
Aggregate valuable and interesting links.
Joyk means Joy of geeK