Serious vulnerabilities in Matrix’s end-to-end encryption have been patched
source link: https://arstechnica.com/information-technology/2022/09/matrix-patches-vulnerabilities-that-completely-subvert-e2ee-guarantees/
Go to the source link to view the article. You can view the picture content, updated content and better typesetting reading experience. If the link is broken, please click the button below to view the snapshot at that time.

A GLITCH IN THE MATRIX —
Serious vulnerabilities in Matrix’s end-to-end encryption have been patched
Previously overlooked flaws allow malicious homeservers to decrypt and spoof messages.
Dan Goodin - 9/28/2022, 4:00 PM

Developers of the open source Matrix messenger protocol are releasing an update on Thursday to fix critical end-to-end encryption vulnerabilities that subvert the confidentiality and authentication guarantees that have been key to the platform's meteoric rise.
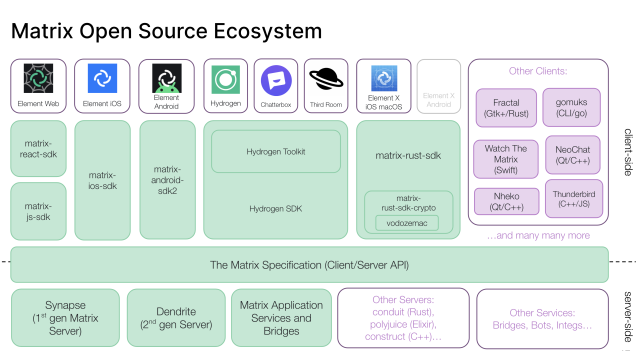
Matrix is a sprawling ecosystem of open source and proprietary chat and collaboration clients and servers that are fully interoperable. The best-known app in this family is Element, a chat client for Windows, macOS, iOS, and Android, but there's a dizzying array of other members as well.
Matrix roughly aims to do for real-time communication what the SMTP standard does for email, which is to provide a federated protocol allowing user clients connected to different servers to exchange messages with each other. Unlike SMTP, however, Matrix offers robust end-to-end encryption, or E2EE, designed to ensure that messages can't be spoofed and that only the senders and receivers of messages can read the contents.
Matthew Hodgson—the co-founder and project lead for Matrix and the CEO and CTO at Element, the maker of the flagship Element app—said in an email that conservative estimates are that there are about 69 million Matrix accounts spread throughout some 100,000 servers. The company currently sees about 2.5 million monthly active users using its Matrix.org server, though he said this is also likely an underestimate. Among the hundreds of organizations announcing plans to build internal messaging systems based on Matrix are Mozilla, KDE, and the governments of France and Germany.
AdvertisementOn Wednesday, a team of researchers published research that reports a host of vulnerabilities that undermine Matrix's authentication and confidentiality guarantees. All of the attacks described by the researchers require the aid of a malicious or compromised homeserver that targets the users who connect to it. In some cases, there are ways for experienced users to detect an attack is underway.
The researchers privately reported the vulnerabilities to Matrix earlier this year and agreed to a coordinated disclosure timed to Wednesday's release by Matrix of updates that address the most serious flaws.
"Our attacks allow a malicious server operator or someone who gains control of a Matrix server to read the messages of users and to impersonate them to each other," the researchers wrote in an email. "Matrix aims to protect against such behavior by providing end-to-end encryption, but our attacks highlight flaws in its protocol design and its flagship client implementation Element."
Hodgson said he disagrees with the researchers' contention that some of the vulnerabilities reside in the Matrix protocol itself and asserts they are all implementation bugs in the first generation of Matrix apps, which include Element. He said that a newer generation of Matrix apps, including ElementX, Hydrogen, and Third Room, are unaffected. There are no indications that the vulnerabilities have ever been actively exploited, he added.
Recommend
-
 175
175
“All official 14.1 builds built after this tweet have been patched for KRACK.”
-
 54
54
“We'll publish critical vulnerabilities in PGP/GPG and S/MIME email encryption on 2018-05-15 07:00 UTC. They might reveal the plaintext of encrypted emails, including encrypted emails sent in the past. #efail 1/4”
-
 24
24
Implementing End-to-End Encryption in Matrix clients This guide is intended for authors of Matrix clients who wish to add support for end-to-end encryption. It is highly recommended that readers be familiar...
-
 4
4
5 VMware products need patching against serious security vulnerabilities VMware urges patching Workspace ONE Access and VMware products that include components of VM...
-
 4
4
Carbon offsets have seriou...
-
 2
2
A Matrix Update Patches Serious End-to-End Encryption FlawsThe messenger protocol had gained popularity for its robust security, but vulnerabilities allowed attackers to decrypt messages and impersonate...
-
 4
4
Overview We report several practically-exploitable cryptographic vulnerabilities in the end-to-end encryption in Matrix and describe proof-of-con...
-
 4
4
Researchers find serious vulnerabilities in cars and emergency vehicles, including BMW, Mercedes, Honda, Nissan, more Attackers could have taken over fleets of police cars and ambulanc...
-
 2
2
Apple says proposed UK law ‘poses a serious threat’ to end-to-end encryption / It joins the operators of other end-to-end encrypted messaging apps like Signal and WhatsApp in expressing concerns about the UK’s Online...
-
 5
5
Post-Quantum Encryption Algorithm KyberSlash Patched After Side-Channel Attack Discovered
About Joyk
Aggregate valuable and interesting links.
Joyk means Joy of geeK