

Solving the Cryptopals Crypto Challenges in C#
source link: https://www.scottbrady91.com/cryptopals/solving-the-cryptopals-crypto-challenges-in-c-sharp
Go to the source link to view the article. You can view the picture content, updated content and better typesetting reading experience. If the link is broken, please click the button below to view the snapshot at that time.

Solving the Cryptopals Crypto Challenges in C#
I’ve recently started the cryptopals crypto challenges, and, frankly, even the basics are kicking my ass. However, I seem to be enjoying them, and I’m finally starting to understand some of the Computer Science topics I really should have listened to at University. If you are like me and prefer learning by getting your hands dirty and hacking some code together, then I highly recommend working through some of these challenges.
If you have not heard about cryptopals before, then I'll leave it to the creators to explain:
We've built a collection of 48 exercises that demonstrate attacks on real-world crypto.
This is a different way to learn about crypto than taking a class or reading a book. We give you problems to solve. They're derived from weaknesses in real-world systems and modern cryptographic constructions. We give you enough info to learn about the underlying crypto concepts yourself. When you're finished, you'll not only have learned a good deal about how cryptosystems are built, but you'll also understand how they're attacked.
The cryptopals crypto challenges
In this series of articles, I’m going to share some of my code and talk through the examples and theory that I found the most useful, hopefully along the way providing some eureka moments to others. These examples are not meant to be the most performant or best-designed code imaginable, but instead as a learning tool that clearly shows the functionality required to solve the challenge.
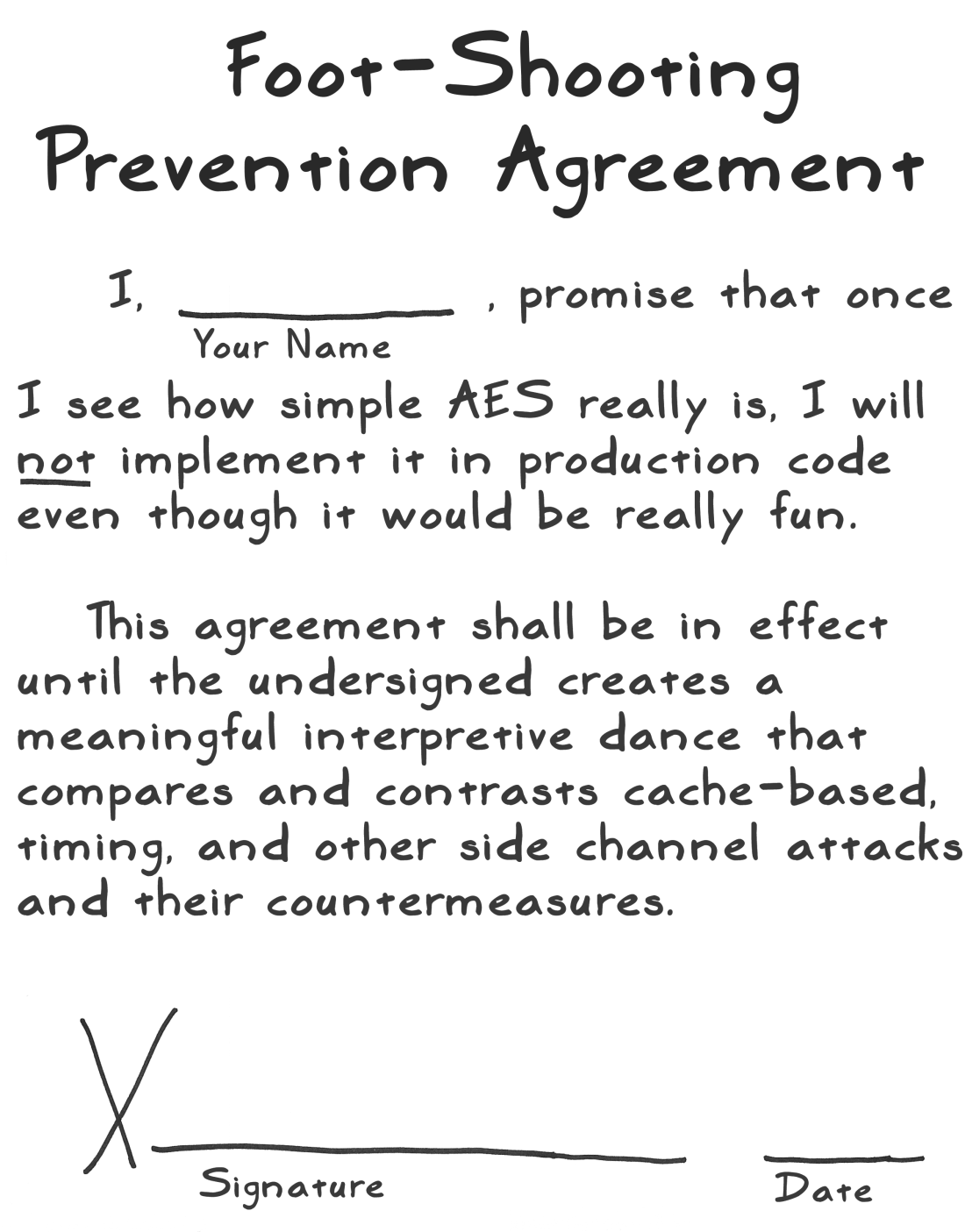
While it is a surprising amount of fun to implement cryptography, here’s a friendly reminder not to use any of this code in production. Stick to reviewed implementations.
 A Stick Figure Guide to AES - Act 3
A Stick Figure Guide to AES - Act 3
All examples were written and tested in C# and .NET Core unless otherwise stated. Most people seem to quit at Challenge 6 or 8, so here’s hoping that I’ll stick with it! Spoiler: I did not.
- Challenge 1: Base64 Encoding in which we implement our own Base64 encoder
- Challenges 2-6: Caesar & Vigenère Ciphers in which we implement and then break XOR implementations of the Caesar & Vigenère ciphers
- Challenge 7: AES in ECB Mode - ready once my brain stops hurting and after my next Pluralsight course...
- Spoilers for challenge 36: Secure Remote Password (SRP) in C# and .NET Core
Favorite Resources
Source Code
These articles discuss the theory and code snippets that helped me the most. For full challenge solutions, check out the accompanying GitHub repository.
Recommend
About Joyk
Aggregate valuable and interesting links.
Joyk means Joy of geeK