

CheeseTools:研究横向渗透和代码执行的工具
source link: https://www.freebuf.com/articles/security-management/276577.html
Go to the source link to view the article. You can view the picture content, updated content and better typesetting reading experience. If the link is broken, please click the button below to view the snapshot at that time.


关于CheeseTools
CheeseTools这个项目基于MiscTool项目创建,可以帮助广大研究人员实现横向渗透和代码执行。
CheeseExec
该工具基于类PsExec功能来实现命令执行和横向渗透,并且必须以特权用户的身份才能运行。该工具主要使用了rasta-mouse CsExec,但是可以允许广大研究人员针对特定的服务或场景创建额外的控制策略:
搜索目标服务是否存在,如果不存在则尝试创建它;
搜索目标服务是否存在或是否终止运行,如果停止运行则尝试启动它,如果不存在则尝试创建并启动它;
搜索目标服务是否存在或是否正在运行,如果是则尝试终止其运行;
搜索目标服务是否存在或是否正在运行,如果是则尝试终止其运行并删除该服务;
命令使用样例
CheeseExec.exe <targetMachine> <serviceName> <binPath> <action>
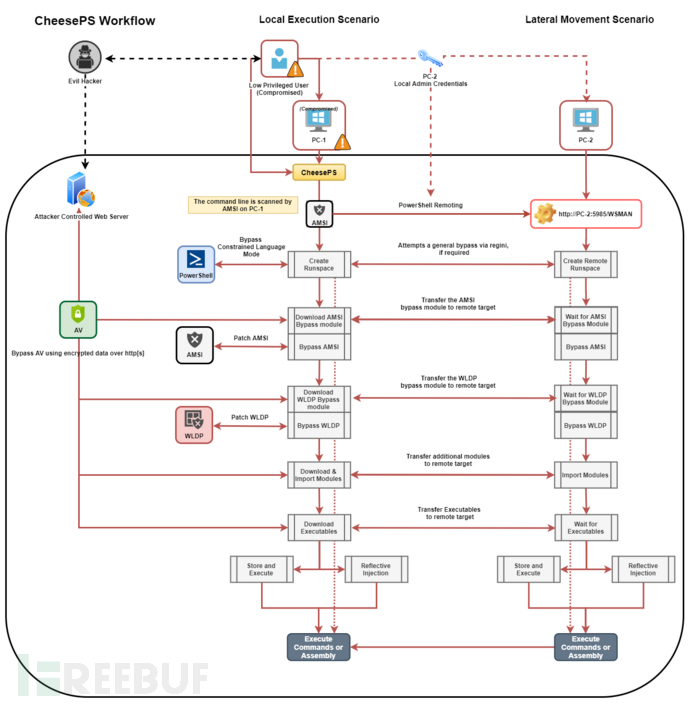
CheesePS
CheesePS是一个命令执行和横向渗透框架,该工组件依赖System.Management.Automation.PowerShell并通过PowerShell来加载和运行任意代码。该工具能够绕过目标主机创建的常见安全限制,并在目标主机上创建和使用PowerShell运行空间,但是此操作必须使用特权用户身份执行。
这个工具最初是作为rasta_mouse CsPosh的增强组件而开发的,但是它本身已经发展成为一个框架,现在可以作为一个通用的PowerShell注入器使用。
工具运行模式
下图显示的是该工具的精确运行模式,可以描述该工具的工作流:
广大研究人员可以使用下列命令将该项目源码克隆至本地:
git clone https://github.com/klezVirus/CheeseTools.git
Usage: -t, --target=VALUE Target machine -c, --code=VALUE Code to execute -e, --encoded Indicates that provided code is base64 encoded -a, --am-si-bypass=VALUE Uses the given PowerShell script to bypass A-M-S- I (fs, smb o http[s]) --aX, --encrypted-am-si Indicates that provided A.M.S.I. bypass is encrypted -i, --import=VALUE Imports additional PowerShell modules (fs, smb o http[s]) --iX, --encrypted-imports Indicates that provided PowerShell modules are encrypted -o, --outstring Append Out-String to code -r, --redirect Redirect stderr to stdout -d, --domain=VALUE Domain for alternate credentials -u, --username=VALUE Username for alternate credentials -p, --password=VALUE Password for alternate credentials -X, --encrypt=VALUE Encrypt a script with an hardcoded key -D, --decrypt=VALUE Test decryption of a script with an hardcoded key -n, --skip-bypass=VALUE Skip A.M.S.I (A), WLDP (W) or ALL (*) Bypass techniques -l, --lockdown-escape Try to enable PowerShell FullLanguage mode using REGINI -w, --wldp-bypass=VALUE Uses the given PowerShell script to bypass WLDP (fs, smb o http[s]) --wX, --encrypted-wldp Indicates that provided WLDP bypass is encrypted -x, --executable=VALUE [Download and] Execute given executable --xX, --encrypted-executable Indicates that provided Exe/DLL is encrypted --xCS, --executable-csharp Indicates that the executable provided is C# - (.NET) -R, --reflective-injection Uses Invoke-ReflectivePEInjection to load the assmebly from memory (requires Invoke- ReflectivePEInjection to be imported!) -P, --powershell-decrypt Force use of PowerShell-based decryption -k, --encryption-key=VALUE Uses the provided key for encryption/decryption --ssl Force use of SSL -h, -?, --help Show Help
跟原生PowerShell相比,该工具有下列显著优势:
更干净、更直观的命令行;
自动化绕过(CLM、AMSI、WLDP);
避免从远程目标执行出站连接(所有内容都通过WS-Management传输);
支持传输中的完全加密;
CheeseDCOM
CheeseDCOM组件可以通过DCOM实现命令执行或横向渗透,但必须以特权用户身份执行该任务。该工具基于rasta-mouse CsDCOM实现,但还添加了额外的方法。当前支持的方法有:MMC20.Application、ShellWindows、ShellBrowserWindow、ExcelDDE、VisioAddonEx、OutlookShellEx、ExcelXLL、VisioExecLine、OfficeMacro。
Usage: -t, --target=VALUE Target Machine -b, --binary=VALUE Binary: powershell.exe -a, --args=VALUE Arguments: -enc <blah> -m, --method=VALUE Methods: MMC20Application, ShellWindows, ShellBrowserWindow, ExcelDDE, VisioAddonEx, OutlookShellEx, ExcelXLL, VisioExecLine, OfficeMacro -r, --reg, --registry Enable registry manipulation -h, -?, --help Show Help
CheeseRDP
该组件可以通过RDI(反射型DLL注入)实现RDP凭证企鹅去,但必须以特权用户身份执行该任务。该组件基于RdpThief实现,但使用了纯C#进行封装,因此可以通过.NET环境运行:
Usage: CheeseRDP [actions] Actions: wait: keep listening*for any new mstsc.exe process indefinitely (stop with ctrl-C) clean: delete the credentials dump file if present dump: dump the content of the file if present, parsing the credentials in a compact format
CheeseTools:【GitHub传送门】
Recommend
About Joyk
Aggregate valuable and interesting links.
Joyk means Joy of geeK